Updated December 2023
One of our New Years Resolutions is to encourage the progressive and radical movements on the Australian continent to get better at digital privacy and security… essentially putting less of ourselves out into the interwebs for our opposition for free
Government and private companies collect data on activists – this has been demonstrated many times over the years. Activists working against fossil fuels are an example of people that have been targeted – innocuous peaceful activities have been reported on by expensive contractors, we have been spied on, had groups infiltrated by police and corporate spies. In the UK, long term undercover policing resulted in women having long term relationships and even children with police spies. Whilst we are not aware of such extreme cases in Australia, it is not something to take lightly, but its also not something that should stop us from acting for social and environmental justice.
The most successfully disruptive aspect of surveillance is encouraging paranoia and making life hard for activists, so don’t let em stop you – you can be the proud owner of an ASIO file along with so many other awesome folk. Guaranteed every high profile activist you have looked up to was probably monitored by the government!
So let’s get the new year off to some good security habits. Here is a quick rundown of some tools that will assist your communications to be more secure. The catch – nothing is fool proof, but getting into good habits, makes for a healthier group culture.
What is security culture – simply a set of practices that limits the ability for government or opponents to find out more information about you and interfere with or monitor your group. We’ve given you some tools to minimise this.
Tech is ever evolving but these are top picks for 2023
- Password manager – honestly, we have no idea how people cope without one these days. You remember one strong password (song lyrics are a helpful idea), and that opens up a secure list of all your passwords, and it can auto generate secure ones also. Lastpass, and Dashlane are quite popular. Keepass is also used (and preferred by some as not cloud based, and open source). Lastpass has a paid version you can have synced to your phone. Read reviews here.
- Protonmail – is a secure email system. You can use it the same as a standard web based email. If you send to a non proton mail account it isn’t encrypted, but protonmail to protonmail is. Its much easier than previous options and is starting to be used by more activists in Australia.
- Signal – is one of the most secure messaging apps – as recommended by Edward Snowden. Still not perfect, but better than most. There are other options such as Wickr, but they don’t share their source code so people can’t check to see if they do what they say. You can read reviews here.
- Virtual Private Network (VPN) The Australian government can now access your metadata. Although metadata access can’t see the contents of your communication – they can see who, and when, and where you were communicating with someone. This can be revealing. The article linked previously includes the chilling statement, “We kill people based on metadata”. The number of companies that have gained access to metadata is also substantial.
We used Nord VPN but found it slow. We now use Vypr and find it quite fast and flexible and it was recommended to us by people who live in countries where human rights defenders are at risk of being killed, and need to obscure information about themselves. Good enough for us. All activists should use a VPN (for phone and computer) that is not connected to a five eyes country (explained more below). This article discusses Australia volunteering to share citizen data as part of the Snowden revelations. Here is another list of VPN options.
- Get off Google. Or at least minimise. Use it only for what you absolutely need. Check out everything google and facebook track! Google directly cooperates with governments, works on military infrastructure contracts and it is based in the United States whose laws regarding digital privacy are very flimsy since the Patriot Act, and have shown to be regularly broken. The five eyes agreement (yes this is real and not a conspiracy theory) means that when countries have laws about spying on their own citizens they just play swapsies with their data. It is one of the organisations detailed by Snowden as part of the Prism surveillance program. Google work directly for and with the US Military. You are literally giving the government full access to your information by using google.
This is damaging as a general habit, but with the level of detail able to be obtained by google, who know what you watch (youtube), search for, read, where you go, how long you are there, your personal habits (google maps and location tracker) – it is a significant amount of data to cross reference about you, and your friends, and fellow activists who you are exposing.
There are no completely equivalent services to the full useability range of google but there are some good compromises.
EDIT (3/20): Complete guide to breaking up with Google
GOOGLE ALTERNATIVES
- Sync is an encrypted cloud service, which is great for storage of static documents, or you can set up a system where you alert each other and date files each time you edit them so versions don’t get mixed up.
- Cryptpad is a shared document editor (encrypted) – with simple capabilities where people can collaborate live on various documents. This has been one of the real stumbling blocks for people trying to de-google, so its great that we have this option now. There is a basic project management tool as well, and you set up an account similar to google drive which will track all your docs.
- Protonmail instead of gmail (as above)
- Keybase is a collaborative platform that allows for conversation threads and storage of documents. It is great for day to day organising, and file storage. It has some similar capabilities to slack
- Brave is a search engine that doesn’t track you.
Private browsing has been around in one form or another since 2005, but it took some time for every browser to get behind it. You can read about that here along with how to do it.
We have deliberately chosen tools that we have used ourselves and found relatively easy. Other lists like this would include encrypting your whole computer, and using Tor. They need a little more explanation. There are other tools out there, but often tools that are designed by digital security geeks, may not be optimised for a lower level of competence. We figure if we can learn this stuff from scratch – anyone can 😊
Rather than being frustrated that safer tools don’t provide the level of ease and capacity that google does, its better to remember that we didn’t always have access to these tools, managed to organise before without them, and consider the very real risk we are opening ourselves up to by handing detailed data and profiles on people over to google, and therefore the government, on a plate. Keeping lists of people who are doing direct action or even low level political advocacy in google places them at risk. We also don’t know how the political situation will change in future, particularly as climate impacts take hold, along with more resource insecurity and unstable governance.
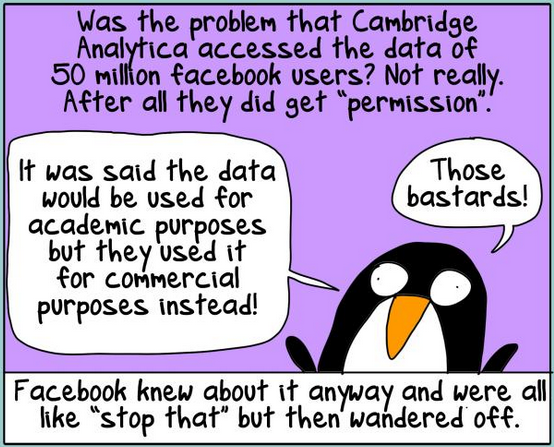
Also, the Australian security services get a very large budget, and very little oversight. Even members of Parliament have gotten little access and understanding of the infrastructure of our surveillance state. Why do the work for them? At least make them work harder for the information on us! We haven’t yet mentioned facebook which is a huge issue in itself, but there are steps you can take to minimise your risk. At a minimum, never use facebook or google as logins to other accounts – it just gives more data for cross reference. There is a project calling for accountability post the Cambridge Analytica scandal and we’ve shared some tips for risk minimisation and a broader list of security resources here.
In Australia NGO’s, progressive and radical groups can be very blasé about data and digital security, and also the duty of care that should come with keeping huge amounts of detailed supporter information safe.
At CounterAct we want to model better practices and encourage people to take digital security more seriously.
Also see:
- Tips for facebook risk management
- See what the internet knows about you (and how to stop it)
- Threat modelling for activists and campaigners
- Privacy tools
- Surveillance self defence
As always – its important to acknowledge that people of colour and Aboriginal activists are more likely be surveilled and treated as a risk by our police and government.
Thanks as always to First Dog who is much better at drawing than us, and has created Brenda the civil disobedience penguin, as our patronus.
Thanks for the post.
Is there a reason 1password isn’t among the password manager options?
It has a nice feature where it will alert you if you have passwords that are among known breaches so you can update them
Hi Chris,
Honestly just because we didn’t want to overwhelm people with tools and wanted to speak to ones we had personal experience with. That is a good feature, might pop it in the list, cheers!